Hey there, digital explorer! So, you've probably heard the buzz about DDoS attacks, right? It’s one of those techy terms that sounds super serious, and, well, it kinda is. But let’s break it down, coffee in hand, no jargon overload, promise! Think of it like this: imagine your favorite online store, the one with all the amazing deals you just can’t resist. Now, what happens if suddenly a million people, all at once, decide to ask the same question to the customer service desk?
Chaos, right? Utter, beautiful, frustrating chaos. That’s pretty much the gist of a DDoS attack, but way more… digital. It’s like overwhelming a system with so much fake traffic, it just throws up its digital hands and says, "Nope, I'm outta here!" So, when you see questions like "Which of the following is true of a DDoS attack?", it’s all about figuring out what’s really going on. Let's dive in, shall we?
DDoS: The Digital Mob
First off, DDoS stands for Distributed Denial of Service. Ooh, fancy! But don't let the big words scare you. "Distributed" just means it's coming from lots of different places. Think of it like a flash mob, but instead of dancing, they’re all trying to jam up a website. And "Denial of Service"? That’s the goal. They want to make a service, like a website or an app, completely unusable for its intended visitors. Like when your internet decides to take a nap right when you’re about to win that game. Annoying, huh?
So, is it like a hacker trying to steal your credit card number? Not exactly. While some cyberattacks are all about data theft, a DDoS attack is more about disruption. It’s like someone parking a truck in front of your business’s entrance. They’re not necessarily breaking in, but they’re definitely stopping legitimate customers from getting in. And sometimes, that’s just as damaging, if not more so, depending on the target. Imagine if your bank’s website went down for hours. That’s not cool, right?
The "Why" Behind the Mayhem
But why would someone do this? Good question! The motives can be as varied as your Netflix recommendations. Sometimes, it’s for activism, a sort of digital protest. They might be upset about a company's policies or a government’s actions. It's their way of screaming, "Hey, pay attention to us!" Sometimes, it's for revenge. Maybe an employee got fired and they’re feeling a bit… unhinged. Or perhaps it’s just sheer malice, a desire to cause trouble for the sake of it. Some people just like to watch the digital world burn, I guess.
Then there’s the fun (not really fun, mind you) of competitors. Imagine a rival online store wanting to take down the competition during a big sale event. That’s a classic move, and super effective if they can pull it off. And sometimes, it’s just a distraction. While everyone's panicking about the website being down, the real bad guys are sneaking in somewhere else, grabbing what they want. It’s like a magician’s sleight of hand, but with more code and less sparkly doves. Seriously, the lengths some people will go to!

How Does This Digital Mob Work?
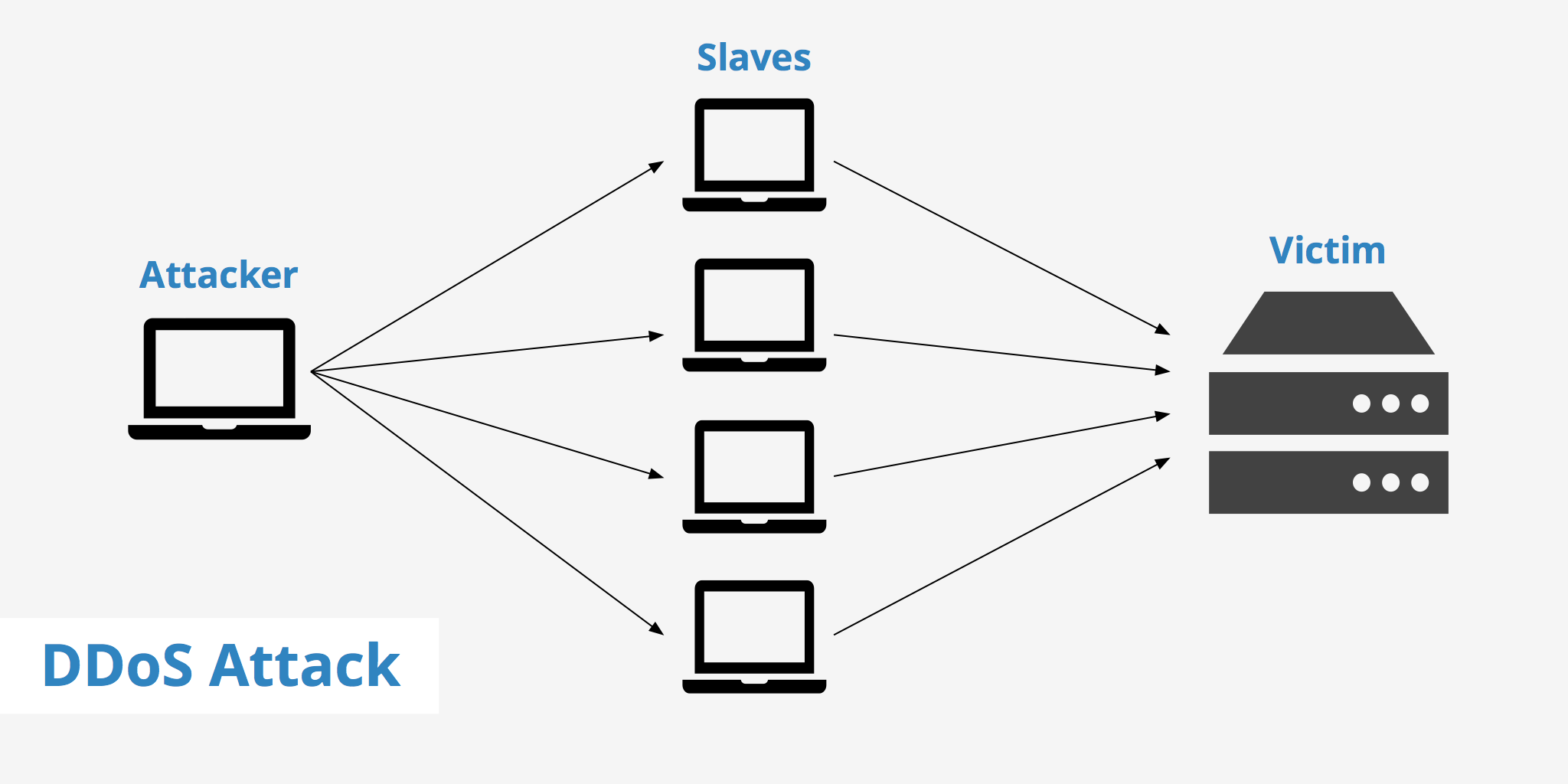
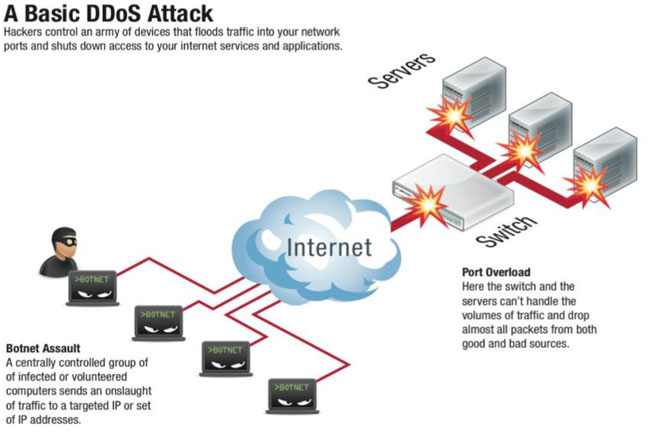
Okay, so how do they actually do it? It’s not like they’re all physically knocking on the server's door. They use something called a botnet. Sounds like a Transformer’s dance crew, doesn’t it? But it’s actually a network of compromised computers, servers, or even those smart devices you have lying around your house (your smart fridge could be part of the problem!). These devices are infected with malware, and they’re all controlled remotely by the attacker, the “botmaster.”
Think of the botmaster as the conductor of a very, very large and very, very naughty orchestra. They send out a command, and all these “bots” (short for robots, obviously) spring into action. They start sending tons and tons of requests to the target server. It’s like a million tiny little paper cuts, but instead of blood, it’s just… overload. The server tries its best to handle all these requests, but it’s simply not built for that kind of insane volume. It gets bogged down, it slows down, and eventually, it just crashes. Poof! Denied service.
The Different Flavors of DDoS
Now, DDoS attacks aren't all just one big blob of digital goo. They come in different shapes and sizes, targeting different parts of the system. We’ve got things like volume-based attacks. These are the brute force ones, aiming to saturate the network bandwidth. It’s like trying to drink a whole lake through a tiny straw. Impossible, right?
Then there are protocol attacks. These target specific weaknesses in the network protocols, like the handshake between your computer and the server. It’s like finding a secret backdoor into a building and just jamming it full of junk. And let’s not forget application layer attacks. These are the more sophisticated ones, targeting specific applications, like your favorite online game’s login page. They’re looking for those tiny cracks, those little vulnerabilities. It’s like a sniper, aiming for a very specific spot. These can be particularly tricky to defend against, because they often look like legitimate traffic, at least at first glance. Sneaky, right?
What Makes a DDoS Attack True?
So, when you’re looking at a multiple-choice question, or just trying to understand the news, what are the key characteristics that scream "DDoS attack"? Let’s nail this down.
First and foremost, it's about overwhelming a target. This is the core principle. It's not about subtle infiltration; it's about flooding. Think of a dam bursting. The sheer volume of water is the problem. A DDoS attack is the digital equivalent of that bursting dam. It’s not trying to pick a lock; it’s trying to break down the whole door with a battering ram. And that battering ram is made of thousands, even millions, of fake requests. So, if an option talks about overwhelming capacity, you’re probably on the right track.
Secondly, and we touched on this, it's distributed. This is crucial. If the attack is coming from a single source, it’s not a DDoS. It's just a denial-of-service attack. The "distributed" part means it’s coming from multiple points simultaneously. This makes it much harder to block, because you can’t just unplug one cable or block one IP address. It's like trying to catch a hundred tiny mice that are all running in different directions. You block one, ten more pop out!
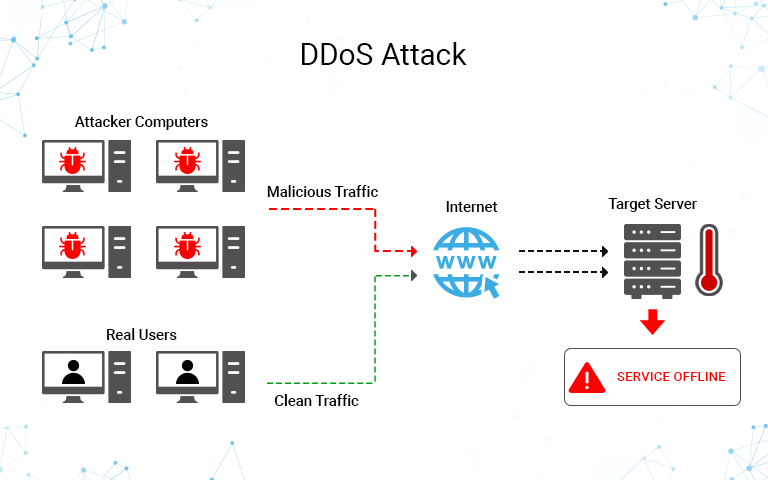
Third, and this is a big one, the goal is unavailability. The attacker doesn't necessarily want your bank account details (though that could be a secondary goal in a more complex scenario). Their primary objective is to make the service unusable. They want to shut it down, make it inaccessible, and cause disruption. So, if the options mention making a website slow, crashing, or inaccessible, that’s a strong indicator. It’s about taking something offline, whether it’s for a few minutes or a few days. Imagine your favorite streaming service suddenly going dark. That’s the impact they’re aiming for.
What's Not a DDoS Attack (Usually)?
It’s also important to know what isn’t typically a DDoS attack. For instance, if someone is trying to gain unauthorized access to your system, that’s usually a different kind of breach. Think hacking into your email or stealing your passwords. That’s about getting in. A DDoS attack is about keeping people out (or preventing the service from functioning for those who are trying to get in).
Also, if the attack involves modifying or deleting data, that’s a different ballgame. While a DDoS attack could be part of a larger, more malicious operation where data destruction is the ultimate goal, the DDoS itself is the act of overwhelming. It’s the noise and the chaos, not necessarily the act of rifling through your drawers and trashing your belongings. Though, sometimes, the chaos is the trashing, metaphorically speaking.
And here’s a subtle but important distinction: if the attack is a single source attempting to overload a system, it's a DoS, not a DDoS. The "distributed" aspect is key. So, if an option describes an attack from just one computer, you can probably cross that one off your list for a DDoS scenario. It’s the coordinated effort from many, many sources that defines it.

The Impact: More Than Just a Glitch
So, what happens when a DDoS attack is successful? It’s not just a minor inconvenience. For businesses, it can be crippling. Imagine a major online retailer during Black Friday being completely offline. That’s millions, maybe billions, in lost revenue. Ouch! And it's not just about money. It's about reputation. If your customers can't access your service, they’re going to go somewhere else. And they might not come back. That trust is hard to rebuild. It’s like if your favorite restaurant suddenly closed for a week without explanation. You’d probably find a new favorite, wouldn’t you?
For individuals, it can mean being cut off from essential services, like online banking or even communication platforms. It’s frustrating, it’s disruptive, and it can make you feel pretty vulnerable. Imagine not being able to check your bank balance before payday, or being cut off from your family during an emergency. That’s the real-world impact of these digital skirmishes.
Identifying the Truths
So, when you’re faced with a question about DDoS attacks, look for the keywords. You want to see things like:
- Massive traffic or overwhelming requests.
- Multiple sources or distributed origins.
- The primary goal being unavailability or disruption of service.
- Often carried out using botnets.
If you see options that describe these phenomena, you’re likely looking at the correct definition of a DDoS attack. It’s all about that overwhelming, distributed flood of digital chaos designed to bring a service to its knees. It’s not always sophisticated, sometimes it’s just pure brute force on a massive scale. And that, my friend, is the essence of a DDoS attack. Pretty wild, huh? Now, let’s go get a refill!